How Cybersecurity Shapes the Future of Technology
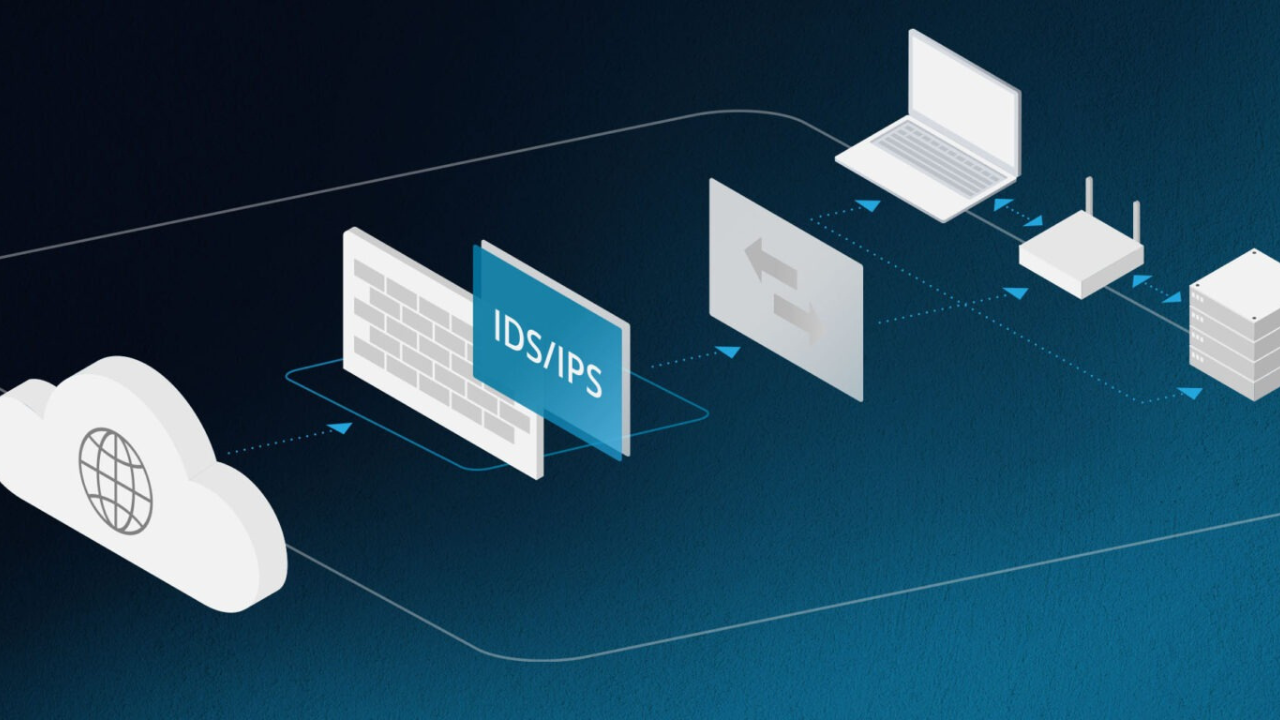
Cybersecurity is shaping the future of technology by moving from a reactive, “bolted-on” afterthought to a proactive, foundational element of design and innovation. As of August 28, 2025, the relentless pressure of sophisticated cyber threats and the growing global demand for data privacy are forcing a fundamental shift: technology is no longer created and then … Read more